
Securing the 5G O-RAN
The wireless communications world is abuzz with excitement over the open radio access network (O-RAN) concept. O-RAN, as we have covered in previous blog entries, promises to spur innovation and lower costs by enabling mobile network operators (MNOs) to build multi-vendor RANs for the first time.
Recently, the topic of O-RAN security has been in the news after the publication of a white paper and subsequent blog post by one of the world’s leading and most influential network equipment vendors, Ericsson.
Before going into further detail about the Ericsson white paper, it’s essential to consider O-RAN's core promise. The O-RAN Alliance — a consortium of 27 global MNOs and more than 180 ecosystem contributors — is the organization that creates the specifications, reference architecture, and the interfaces between the various subcomponents that form O-RAN. The core principles of the O-RAN Alliance are openness, intelligence, virtualization, and interoperability.
The Ericsson white paper, “Security Considerations of Open RAN,” points out that moving from a closed, proprietary RAN to an open RAN introduces new potential vulnerabilities and increases the attack surface of a network. Opening any system, by definition, can potentially make it more vulnerable from a security standpoint.
The O-RAN architecture adds many new interfaces as well as the incorporation of the 5G-XHaul transport to connect small cells to the core network, all of which increase the security attack surface of the RAN. In addition, O-RAN’s intelligent non-real-time/near-real-time RAN intelligent controller (RIC) adds new complexities such as potential xApps conflicts and root of trust concerns. And, finally, O-RAN’s deployment on a virtualized or cloud-native environment adds additional layers of security issues, such as infrastructure, container, and cluster security, among others.
As the Ericsson white paper argues, these potential vulnerabilities underscore the need for security best practices and robust security standards. They also make the case for rigorous O-RAN security testing.
Security cannot be an afterthought or something bolted onto an O-RAN. Security must be a primary consideration from the beginning. Keysight believes in implementing security best practices throughout the process of realizing 5G O-RAN implementation, from design, development to manufacturing, through the supply chain, deployment, and operation. Keysight’s test and measurement portfolio covers end-to-end functional, performance, and security testing from the RAN to the 5G network core.
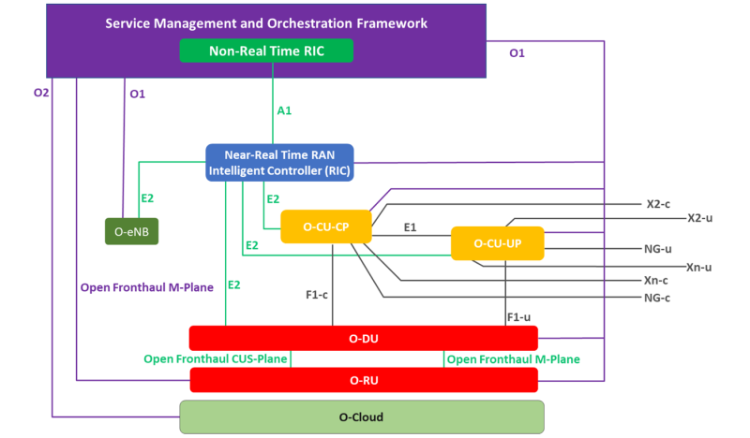
O-RAN security can be broken down into four categories: O-RAN subcomponent security, XHaul transport security, RIC security, and O-Cloud security. When it comes to protecting the O-RAN from vulnerabilities, no one category is more important than another. A chain is only as strong as its weakest link.
Implementing rigorous O-RAN security testing also calls for accredited 3rd party audits and continuous or automated testing where applicable.
In support of its mission to accelerate innovation to connect and secure the world, Keysight’s security team has been diligently working on 5G/O-RAN-related security research and testing solutions. As a trusted vendor and thought leader in 5G security, Keysight is active on many fronts. These include participation in:
- 3rd Generation Partnership Project (3GPP) SA3 security assurance specification
- O-RAN Alliance Workgroup 1 focused on security test specifications
- The Open Test and Integration Center (OTIC) jointly operated by the O-RAN Alliance and the Telecom Infra Project (TIP)
With the O-RAN movement in full swing, the wireless communications industry is entering a brave new world. O-RAN implementation will bring innovations and a reduction in cost. But it will also bring new complexity and potential security threats. Robust security practices, standards, and testing are essential to realizing the promise of open RAN.
Related blog entries:
Related white paper:
For more information on 5G and Keysight's 5G portfolio, please visit the following webpages:
- Keysight's 5G Chipset Manufacturers webpage
- Keysight's 5G Device Manufacturers webpage
- Keysight's 5G Network Equipment Manufacturers webpage
- Keysight's Service Providers' webpage